Advanced Persistent Attack - How To Secure My Computer From APT
IT experts need to know how to
react to advanced persistent threats, which speak to real cybersecurity dangers
for undertakings.
For quite a long time, data
security groups have constructed a progression of natural controls intended to
ensure against recognizable threats. Firewalls, hostile to malware programming
and interruption discovery frameworks all effectively kept most aggressors
under control. Yet, the threat scene has developed fundamentally, with modern
aggressors and assault strategies showing up on the scene. While endeavors
ought not disregard conventional security controls, they should consider
advances and measures that ensure against these more refined threats.
These new assailants, known as advancedpersistent threats (APT), speak to a noteworthy hazard to cybersecurity. APTs
earned their name since they use advanced assault methods in a think way,
engaged against very much characterized targets. Dissimilar to easygoing
assailants who essentially look for undefended focuses of chance, APTs select
their objectives in view of particular knowledge social affair or framework
interruption destinations. They at that point direct surveillance against those
objectives and level exact, directed assaults intended to accomplish their
goals rapidly, effectively and stealthily.
Read More: Pop up ads
APTs are normally very much
financed endeavors sorted out by governments, military associations and
nonstate on-screen characters, for example, composed wrongdoing. They enlist
gifted architects and cybersecurity specialists who create tweaked assaults
that endeavor beforehand obscure vulnerabilities. Known as zero-day assaults,
these are particularly deceptive for two reasons: First, since they are
obscure, merchants have not yet discharged patches to rectify them. Second,
signature-based location frameworks are feeble to recognize them on the grounds
that there are no marks for these obscure assaults.
A current report by the Ponemon
Institute and the Information Systems Audit and Control Association (ISACA)
gave stark measurements about the readiness of ventures to react to APT
assaults. While 49 percent of ventures studied thought of it as
"likely" that they would be the objectives of an APT, just 15 percent
expressed that they were "exceptionally arranged" to manage an APT
assault. Associations trying to react to APTs require a powerful toolbox set up
that will enable them to rapidly distinguish, dissect and react to modern
cyberattacks. These abilities will restrain the disturbances caused by
assaults, enabling associations to return to business rapidly.
Also Read: Conficker
THE THREAT OF STEALTH
A standout amongst the most
harming attributes of APT assaults is their capacity to stay undetected for
drawn out stretches of time. Media reports flourish of expansive associations
that have endured refined assaults, yet just identified them weeks or months
after interlopers invaded their systems and frameworks. These assaults are
especially hazardous on the grounds that they give the culprits progressing
access to touchy data and in addition the capacity to cover their tracks and
upset security endeavors that may identify the penetration.
In May 2015, the Ponemon
Institute discharged an exploration report contemplating APT assaults against
the retail and money related administrations enterprises. The investigation
uncovered that broke retailers took a normal of 197 days to distinguish an APT
interruption, while monetary administrations firms took 98 days to identify an
assault. When they recognized assaults, firms in the two classifications took
roughly a month to contain the harm: 26 days for money related administrations
firms and 39 days for retailers. That is a hazardously drawn out stretch of
time for a system to remain bargained.
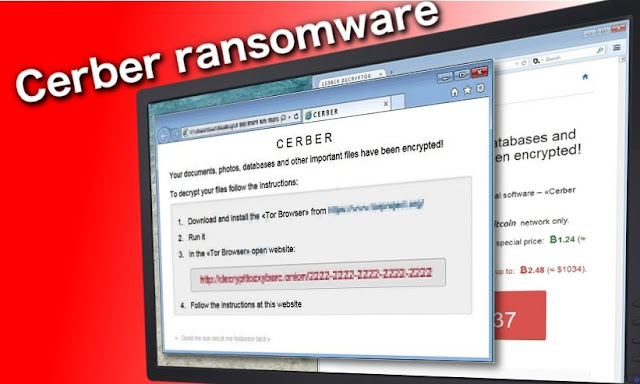
Read More: Ransomware Removal Tool
Chinese APT group steals code-signing certificates
An advanced persistent
threat (APT) assemble situated in China, code-named Suckfly, has been
disguising its accursed action in the course of recent years by taking
code-marking testaments and applying them to malware and hack devices to
influence them to look like true blue programming when downloaded.
Also Read: https://freeadwareremovaltool.wordpress.com/2017/11/10/advanced-persistent-threat-how-to-remove-apt/
As indicated by a
security blog entry by Symantec, Suckfly stole the endorsements from true blue
organizations in Seoul, Korea and utilized them to conceal assaults against
overall government and business substances starting in mid 2014. Symantec wound
up noticeably mindful of this plot in 2015 subsequent to finding a hacking
apparatus utilized against one of its customers was marked with an endorsement.
Suckfly's digital
armory incorporates keyloggers, accreditation dumpers, port scanners and
indirect accesses, including one custom secondary passage named Nidiran
particularly produced for digital secret activities crusades. Symantec followed
the APT's movement to three IP addresses in Chengdu, China.



Comments
Post a Comment